I have been playing with the Azure Access control solution and how to put an application into the Azure Marketplace SaaS offering. The first issue I ran into was getting ACS to work. I had developed a solution with Microsoft’s Active Directory Federation services 2.0 before some the concept was familiar to me. Even through the topic was familiar to me federation errors are often still a pain to resolve.
The first thing you have to do is understand if the error is coming from the provider or client. In this case even though ACS is throwing the error the error is actually coming from the client as it is rejecting the token. It can be rejecting the token for a few reasons.
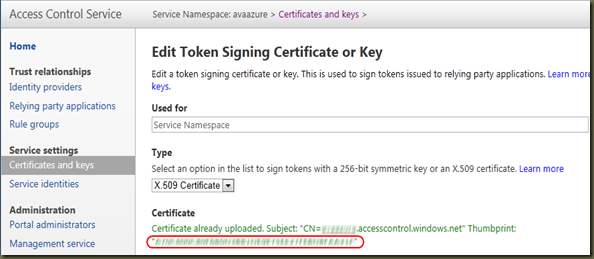
1) The certificate thumbprint the website is looking to validate against does not match. Check the sites web.config trusted issuers section and make sure the thumbprint matches what ACS has.
<issuerNameRegistry type="Microsoft.IdentityModel.Tokens.ConfigurationBasedIssuerNameRegistry, Microsoft.IdentityModel, Version=3.5.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35"> <trustedIssuers> <add thumbprint="[yourthumbprint]" name="[yournamespace]" /> </trustedIssuers> </issuerNameRegistry>
Here is where you get the thumbprint from in the Azure ACS
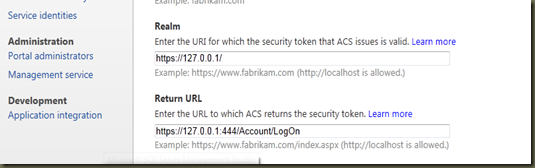
If that does not work your wreply URL back to your website is not correct.
2) Check that the URL the token is being issued for (based on the wreply url) matches the audience URI configured in your application.
In my case I was in my development environment and therefore using odd port numbers. Once I updated the return URL so it had the port number of 444 and the audience URI in my web config to match it worked.
Comments